Describe the Zero Trust adoption framework and rapid modernization plan
Implementing Zero Trust across an organization is a major transformation that requires a structured approach beyond deploying individual technologies. The Zero Trust adoption framework provides strategic planning guidance for this transformation.
Zero Trust adoption framework
The Zero Trust adoption framework helps organizations plan and execute a Zero Trust strategy across their entire digital estate. It adapts the lifecycle phases from the Cloud Adoption Framework for Azure to the unique scope of Zero Trust—introducing new security configurations across an entire digital estate rather than onboarding individual workloads.
Adopting a Zero Trust strategy requires buy-in from across the C-suite. Security isn't the responsibility of one team—it's a shared business responsibility aligned to business outcomes. Each C-level role has a stake in Zero Trust, from the CEO who needs an integrated approach to security, to the CFO who needs measurable accountability for security spend.
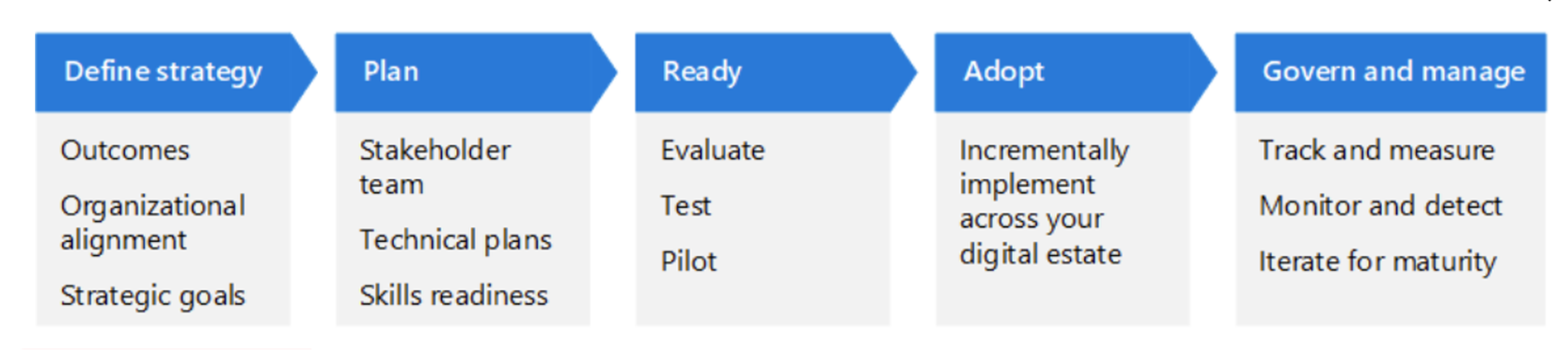
The framework organizes adoption around a lifecycle with five phases:
| Phase | Description |
|---|---|
| Define strategy | Build a business case focused on the outcomes most closely aligned with your organization's risks and strategic goals. |
| Plan | Prioritize quick wins and incremental progress. Structure coherent initiatives with clear outcomes, benefits, and ownership. |
| Ready | Evaluate, test, and pilot security configurations. Prioritize early actions based on business needs. |
| Adopt | Incrementally implement the strategy across functional areas. |
| Govern and manage | Track and measure the success of your deployment. Use monitoring and detection technologies to incrementally mature each functional area. |
Business scenarios
The framework applies the lifecycle through business scenarios that break work into concrete objectives. Each objective is a technical project that moves through the lifecycle independently, and you can stagger objectives so multiple workstreams progress in parallel. The framework includes these business scenarios:
- Rapidly modernize your security posture: Build the organizational capacity and basic security hygiene needed for every other scenario.
- Secure remote and hybrid work: Apply Zero Trust protections to identities, devices, and applications for remote access.
- Identify and protect sensitive business data: Discover, classify, and protect sensitive data across your digital estate.
- Prevent or reduce business damage from a breach: Limit blast radius through segmentation, threat detection, and response capabilities.
- Meet regulatory and compliance requirements: Align Zero Trust protections with regulatory frameworks and track compliance status.
The Rapidly modernize your security posture scenario is typically the starting point because it builds the organizational capacity—strategy alignment, risk assessment, security hygiene, and a repeatable adoption process—needed to systematically execute the other business scenarios. In turn, the other scenarios supply the technical objectives that feed through this process and accelerate the overall transformation.